Securing the Agentic Economy: Inside AetherNet's Post Quantum E2EE Architecture
AetherNet is Kronova's answer: a zero-trust, bare-metal settlement architecture built entirely on finalized NIST post-quantum standards.

! Executive Summary
The transition to agentic commerce is no longer a theoretical horizon — it is an active infrastructure shift. As autonomous AI agents begin negotiating, transacting, and settling financial mandates on behalf of enterprises, the underlying communication layer faces a catastrophic threat: legacy cryptography.
Standard RSA and ECC encryption protocols are fundamentally insufficient against "Harvest Now, Decrypt Later" quantum attacks. AetherNet is Kronova's answer: a zero-trust, bare-metal settlement architecture built entirely on finalized NIST post-quantum standards — FIPS-203 ML-KEM, FIPS-204 ML-DSA, and Rust-based Trusted Execution Environments.
The Threat: "Harvest Now, Decrypt Later"
If an AI agent is transmitting proprietary corporate treasury strategies or Protected Health Information (PHI) to a settlement network today, that payload requires mathematical guarantees that extend decades into the future. Nation-state adversaries are already harvesting encrypted traffic at scale, holding it until sufficiently powerful quantum computers arrive to decrypt it retroactively.
Current API security relies heavily on transport-layer security (TLS) terminating at an intermediary proxy. In an agentic network, intermediaries cannot be trusted with plaintext financial intents. Four structural vulnerabilities compound the threat.
TLS Terminates at the Proxy
Standard API security decrypts at the intermediary before re-encrypting
In an agentic network, no intermediary can be trusted with plaintext financial intents. Every proxy hop is a potential harvest point for a patient, quantum-capable adversary collecting today's ciphertext for tomorrow's decryption.
ECC and RSA are Quantum-Vulnerable
Shor's algorithm solves the discrete logarithm problem underpinning both
Today's TLS handshakes will be decryptable by sufficiently powerful quantum hardware. Any payload secured with ECC or RSA today is a retroactive liability within a decade.
No Agent Identity Standards Exist
No cryptographic mechanism validates authorized autonomous agents today
Current infrastructure has no mechanism to validate that a transacting party is an authorized autonomous agent rather than a malicious impersonator or prompt-injection attack vector.
MCP Payloads Are Plaintext in Transit
Model Context Protocol assumes a secure transport that does not yet exist
MCP defines the payload structure but has no native E2EE. Every tool call, every context object, and every financial intent is readable at every hop between originating agent and destination.
The solution is architectural, not incremental: AetherNet enforces true E2EE by ensuring the payload is sealed by the transmitting agent and only ever decapsulated inside the recipient's secure enclave — using finalized NIST standards throughout the entire chain.
The Solution: The Post-Quantum Envelope Architecture
AetherNet implements the official FIPS-203 ML-KEM standard natively in the SDK. Every mandate travels sealed from origin to TEE — no intermediary can read it at any point in transit.
Asymmetric Encapsulation
FIPS-203 ML-KEM — Module-Lattice Key Encapsulation
The transmitting agent uses the public ML-KEM key of the destination TEE to generate a mathematically binding ciphertext and a 32-byte shared secret. The private key never leaves the recipient enclave. Only the intended autonomous model can perform decapsulation — no proxy, no intermediary, no exception.
NIST security level 5. 1568-byte ciphertext. Equivalent to AES-256 against both classical and quantum adversaries.
The encapsulation output is known only to the transmitting agent and the destination TEE. It never travels across the network in any readable form.
Fresh encapsulation per mandate guarantees forward secrecy — compromise of one session key does not expose past or future sessions.
Symmetric Payload Encryption
AES-256-GCM — Authenticated Encryption with Associated Data
The actual payload — a block trade execution, a healthcare claim, a treasury mandate — is encrypted via AES-256-GCM using the 32-byte shared secret from Step 1. GCM mode generates a 16-byte authentication tag and a 12-byte IV, providing both confidentiality and integrity in a single pass.
The 16-byte GCM authentication tag detects any single-bit modification to the ciphertext. A tampered payload is rejected before decryption is attempted.
The MCP payload never travels as plaintext across any network hop. Only ciphertext, IV, and authentication tag are transmitted — readable by no intermediary.
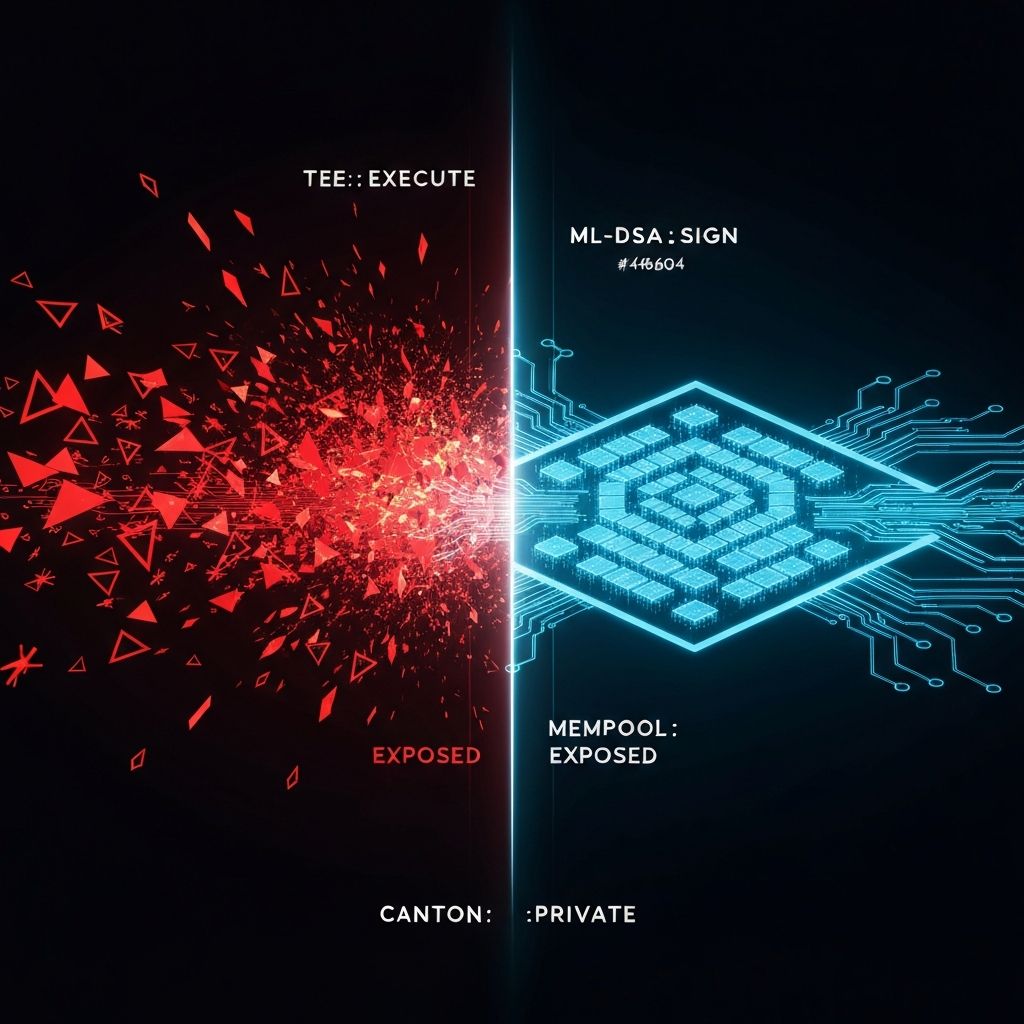
The FIPS-204 Envelope Signature
ML-DSA — Module-Lattice Digital Signature Algorithm
The entire sealed envelope is signed using FIPS-204 ML-DSA to prove the agent's identity and mandate intent. This 4627-byte signature is quantum-resistant and unforgeable. The TEE validates it before decapsulation begins — a tampered identity causes immediate discard.
The trust model: If the agent's identity or mandate intent has been tampered with at any point in transit, the ML-DSA signature check fails and the envelope is discarded without ever reaching the settlement engine.
Legacy Cryptography vs. AetherNet PQC Standards
| Property | RSA / ECC | AetherNet PQC |
|---|---|---|
| Key Exchange | ECDH (quantum-vulnerable) | FIPS-203 ML-KEM-1024 |
| Payload Encryption | AES-128 (adequate today) | AES-256-GCM (quantum-hardened) |
| Digital Signature | ECDSA (quantum-vulnerable) | FIPS-204 ML-DSA-87 |
| Harvest-Now Risk | Critical — decryptable in future | Eliminated — lattice-hard problem |
| TLS Integration | TLS 1.3 (ECDHE key exchange) | TLS 1.3 + ML-KEM ephemeral |
| Execution Environment | User-space process | Hardware Rust TEE (memory-safe) |
| NIST Standard | Pre-quantum era | FIPS-203, FIPS-204 (2024) |
The Foundation for Agentic Commerce
We are not just building a payment protocol; we are building the required cryptographic primitives for the next generation of the internet. By open-sourcing the Kronova SDK, we are giving developers the tools to instantly drop quantum-proof, SMART on FHIR compliant authentication and secure envelope routing directly into their Next.js and Node environments.
Only at the exact microsecond of decapsulation — deep inside the memory-safe confines of the Rust TEE — does the payload become readable plaintext. There is no window, no exception, and no API endpoint through which the decrypted data escapes the enclave boundary before reaching the settlement engine.
"The agentic economy requires determinism, zero-trust routing, and post-quantum secrecy. With AetherNet, that infrastructure is officially live."
The future of autonomous agent commerce is not built on legacy TLS. It is built on lattice-hardened cryptographic envelopes, hardware-isolated execution, and NIST-standardized post-quantum primitives. AetherNet delivers all three — in production, today.
Deploy Post-Quantum E2EE Today
AetherNet is accepting select partners for our Q2 2026 private alpha. If you require quantum-proof, zero-trust agent communication infrastructure for institutional or regulated deployments, contact Kronova today.